Cookies Notice
This site uses cookies to deliver services and to analyze traffic.
📣 Introducing AI Threat Modeling: Preventing Risks Before Code Exists
DevOps is a continuous process for developing, deploying, and managing applications across the software development lifecycle (SDLC). A DevOps team champions automation, stability, and efficiency, but DevSecOps is the security backbone that supports risk remediation in a DevOps environment.
In an automated SDLC, DevOps is an umbrella term that defines the way code is integrated, tested, and deployed, and DevSecOps means integrating security into the DevOps process to protect your applications and infrastructure. DevSecOps platforms reduce cybersecurity overhead for your security operations and more quickly and efficiently find vulnerabilities and misconfigurations – allowing you to remediate critical risks before deploying to production.
DevOps and DevSecOps are often used to develop, deploy, and secure cloud-native applications, which have unique and complex security challenges.
DevSecOps enables effective collaboration between Development, Security, and Ops and empowers individuals to “bake security in” as early as possible in the SDLC.
In a traditional development environment, developers commit code that is then manually promoted to production after a testing process. A code promotion date is often set for a specific release and code is promoted weekly or monthly based on an organization’s deployment schedule. This traditional SDLC slows down release of new updates and features, making users wait for important changes and delaying important bug fixes.
Today, code promotion can be completely automated. This evolution in the software development lifecycle led to DevOps, which is a team of developers and operations staff who come together to improve the velocity of software development and deployment. Usually, DevOps is associated with cloud-native or containerized environments where code is dissected into smaller repositories rather than one large monolithic codebase. However, automation has touched even traditional coding environments and specific tools (e.g., Jenkins) have been developed to support almost any environment with automation.
Many organizations have adopted the Continuous Integration / Continuous Delivery (CI/CD) model as an essential component in efficient SDLC automation. The benefits are clear and compelling. For example, Netflix reports that it takes only 16 minutes from code commitment to deployment in the cloud.
With increased development velocity come security challenges. A DevOps environment has many moving parts, and each unmonitored and unchecked component adds risk to the environment. With rapid development and code deployed to production immediately after it is committed, organizations need an added layer of security, conveniently named DevSecOps. DevSecOps is the security automation built into a DevOps environment. It stands for Development, Security, and Operations.
Every organization has their own unique DevOps environment using specific tools and standards that meet their business requirements. Some organizations use automation to test and commit code to a staging environment but still use manual code deployments. Regardless of the environment, DevSecOps reduces the risk of deploying unforeseen vulnerabilities to production.
Cloud-native applications can be complex, so DevSecOps needs to identify, prioritize, and remediate risks across the SDLC, from design flaws to Infra-as-Code misconfigurations, hardcoded secrets, vulnerabilities, architecture drifts & software supply chain threats.
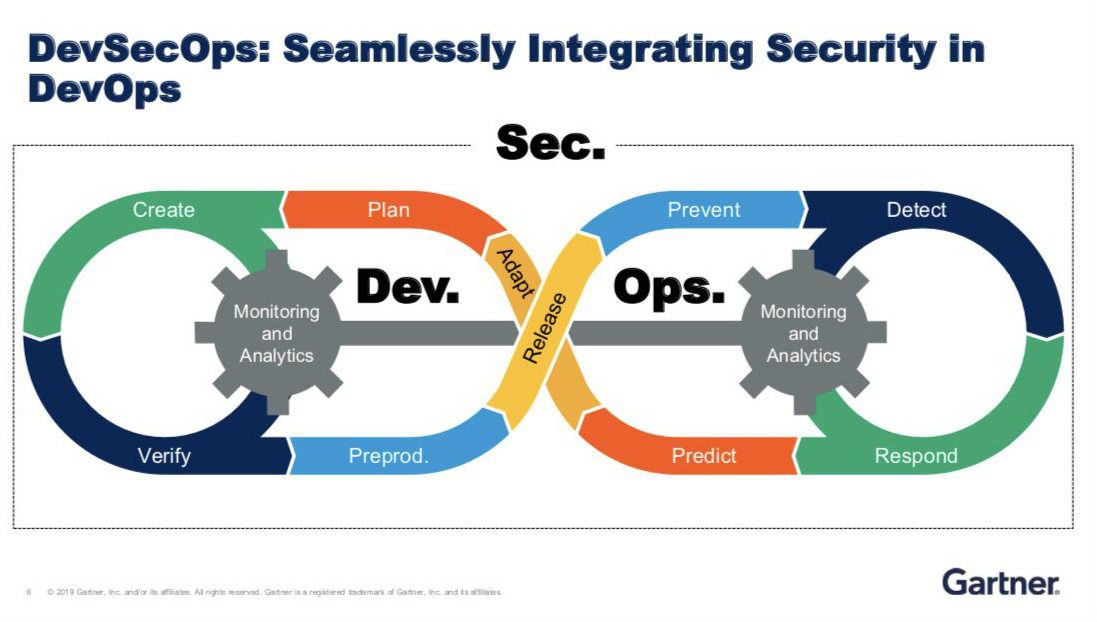
Figure 1. The Gartner DevSecOps Framework (Source)
Good DevSecOps works seamlessly with your DevOps tools and automation strategies. It streamlines security processes to remove unnecessary roadblocks and improve DevOps processes to continue to accelerate software delivery. DevSecOps uses a number of common tools and it provides several ways to improve security across all applications. Some of these DevSecOps methods ensure that your organization stays compliant and has the infrastructure necessary to maintain a low-risk environment for customers and your own sensitive data. These tools and methodologies help developers and operations people make informed decisions. DevSecOps programs must remediate a number of security risks, including:
Code Vulnerabilities: A Static Application Security Testing (SAST) tool promotes secure coding during the development of an application. Developers use their favorite development tool (e.g., Visual Studio) to create their code and compile it to test it as they go along. A SAST tool scans the source code as a developer creates their code. Several tools will check for potential bugs, but a security scanner will specifically find security vulnerabilities before the code is compiled. SAST will also scan the codebase before it’s compiled and shipped to production. Developers benefit from a SAST tool by fixing vulnerabilities before they reach a repository, or they can roll back committed changes so that they can remediate any found vulnerabilities and leave the codebase intact.
An effective SAST will find several critical vulnerabilities such as SQL injection, cross-site scripting (XSS), buffer overflows, and others. It’s an important step in defense against unforeseen vulnerabilities that many developers are unaware of when they commit code to a central repository.
The issue with legacy SAST scanners is high false-positive rates, which are typically 80% out-of-the box but can only be lowered down to ~40% with continuous configuration and fine-tuning.
Misconfiguration detection: Operations professionals provision hardware for developers to deploy their software. Whether infrastructure is local or in the cloud, provisioned resources must be configured properly. Misconfigurations are a common source of data breaches where organizations disclose sensitive information based on one simple yet critical configuration error. Recent studies show that 46% of AWS S3 buckets may be misconfigured, allowing for full disclosure of any stored data to any threat actor.
For example, DevSecOps tools will scan provisioned resources to determine if any misconfigurations leave sensitive information publicly exposed. These vulnerabilities are often left open for months before an organization detects them, and by then terabytes of customer and employee data may have been exfiltrated.
Exposed secrets: With the rising popularity of cloud-based repository tools such as GitHub, passwords, OAuth tokens, and private keys stored in cleartext files is a growing security issue in development environments. Developers hardcode secrets and keys in their code to work with external APIs and systems, but then forget to remove them when uploading code to publicly available repositories, leaving accounts open to a compromise, takeover, and abuse.
GitHub warns developers after potential secrets are found, but a simple search for “removed AWS key” on the GitHub platform will result in thousands of repositories open to potential account takeover and abuse. DevSecOps will find these potential vulnerabilities and warn developers and administrators that secrets were found in the public code.
Software supply chain vulnerabilities: Supply chain attacks are often complex, so they are often sophisticated threats created for corporate espionage, malware injection or large data breaches. Third-party tools and hardware are used for a myriad of solutions from adding application functionality quickly to a software product or for building hardware infrastructure within a data center.
In software supply chain attacks, malicious code can be added silently in an important library or software third-party component. Once added to a targeted victim’s codebase or injected into one of the steps of the build process, the malicious code can perform numerous actions such as skimming credit card numbers, sending sensitive data to an attacker-controlled server, or cryptojacking.
Because DevSecOps is automated, organizations get continuous scanning and detection of critical application risks, and most tools will alert developers and administrators in real-time so that they can act quickly. DevSecOps tools and processes are more than vulnerability scanners. They allow stakeholders to make quick, informed decisions to remediate risks early in the SDLC.
Critical risks can come from vulnerabilities or misconfigurations at the design, in the code, or in production cloud environments. No single scanning tool will ever be able to fully eliminate risk, so you still need continued assessment and identification of both code and production vulnerabilities. For example, a logic error in a production application could trigger a system failure that allows for unauthorized access to data. This error might not be discovered during testing and SAST scanning, but a DevSecOps tool will continuously scan and discover missed vulnerabilities in production.
DevSecOps programs ultimately provide the following benefits:
Many organizations have already built a DevSecOps program through trial and error. To avoid common pitfalls, an organization can follow best practices that will ensure success. The goal of any DevSecOps strategy should be to reduce risk and support developers in their coding procedures but stop any potential vulnerabilities from being introduced on the system.

Figure 2: Integrating security into DevOps
Adopt the concept of “shift left” for security. Shifting left means identifying and remediating risks as early as possible in the SDLC. Traditionally, security assessments were performed when application code was deployed to staging – or even production! This results in extensive re-work when security issues are uncovered, leading to reduced efficiency and high costs.
A “shift left” methodology speeds up development by providing notifications before a developer commits code and deploys it to staging, so it eliminates several steps in the development process. The organization has fewer vulnerabilities deployed to production, and security issues are addressed immediately, putting cybersecurity on the forefront of development and improving your security posture.
Better education for developers. Feedback from security tools let developers know that vulnerabilities exist in their code. This helps them understand the importance of secure code and provides valuable feedback on coding mistakes so that they can make better code and design decisions in the future.
Always use tracing and monitoring. Monitoring is essential to compliance and tracing helps with error detection and analysis. Good DevSecOps monitors the environment for any changes or errors that could lead to a data breach. It gives more visibility across the environment so that developers and administrators can take swift action and contain potential threats after detection.
Continually perform risk assessments on production applications. Application security shouldn’t end after code deployment. A configuration change in the cloud infrastructure may introduce critical risks that are not detectable by looking at the code alone. DevSecOps must ensure discoverability and monitoring of application assets from design through production.
Automated environments are fast-paced and rapid changes can lead to unforeseen bugs and potential vulnerabilities. Making a monitoring system a part of your DevSecOps strategy ensures that bugs and vulnerabilities are caught quickly even if they slip through the cracks in development and staging.
Keep communication between teams flowing. Everyone on the DevSecOps team from developer to CISO should be on board with a secure approach to development. Not every environment is perfect for every member of the team, but you can foster a better and secure approach to the SDLC when every team member is aware of its importance. Communication, education, and training will build a team that sees the bigger picture when it comes to cybersecurity, threats, and risk assessment.
Monitor, review, and optimize frequently. As new technology is introduced and the environment grows and changes, it might be time to revisit your DevSecOps strategy to ensure that it covers all aspects of your software development lifecycle. Current strategies should be continuously reviewed to ensure that they are optimized to the full extent. In the beginning of a strategy’s implementation, you might need to review your DevSecOps plan more frequently. Continual optimization of your DevSecOps processes will ensure that security of application code is always covered.
Use a DevSecOps platform to fully integrate security into development. Platforms break down difficult barriers to allow developers and operations people detect vulnerabilities faster. Code is deployed faster and fewer critical security patches are needed from developers, reducing stress on your staff. Instead of manually performing risk assessment, a DevSecOps platform discovers risks for you and makes it easier to manage.
You can find a simple scanner to find vulnerabilities, but you’ll find yourself overwhelmed investigating false positives and alerts that don’t present a true threat to your organization. A DevSecOps platform identifies critical risks, improves efficiency, and reduces overhead for your security staff and developers. A platform will integrate with your CI/CD pipelines so that you have complete coverage from code creation to the production environment.
In a highly agile environment, it’s virtually impossible to discover and monitor every moving part. An integrated platform will discover assets, tie into your code creation with a SAST, monitor cloud infrastructure as code, and detect potential vulnerabilities in container configurations and orchestration tools (e.g., Kubernetes).
Instead of scanning assets after they’ve sat in production for months, a DevSecOps platform runs security vulnerability scans at the very start of software development. Find a solution that will give you a context-based risk graph to help everyone on your team understand and quickly remediate critical risks.
DevSecOps is essential to securing cloud-native applications. It is the logical evolution of Application Security to automatically and continuously identify risks and enable AppSec professionals to remediate issues earlier in the SDLC.