Powered by Deep Code Analysis (DCA)
Bridge the gap between source and application runtime
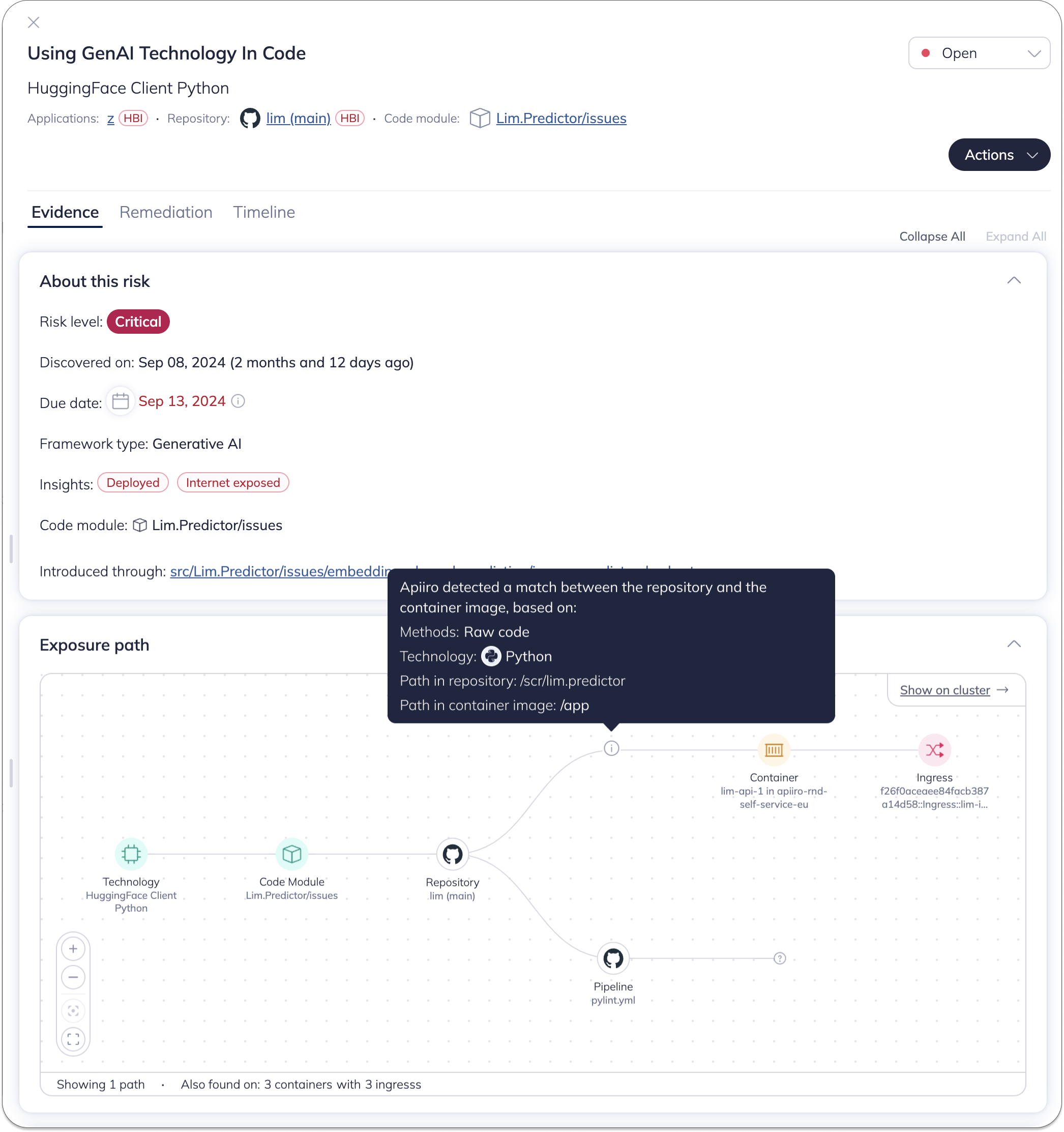
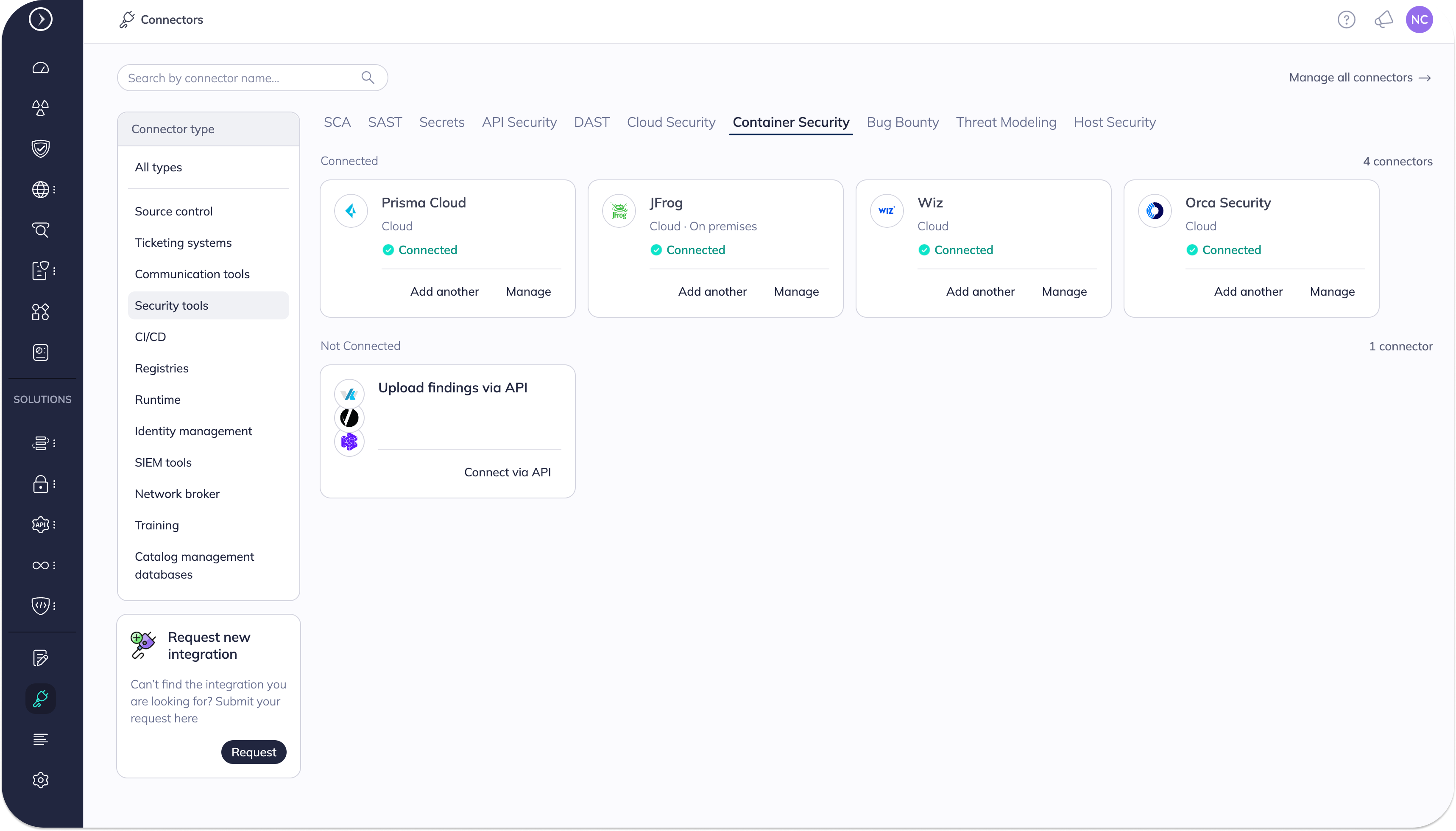
Apiiro’s innovative Code-to-Runtime Matching Technology uses Deep Code Analysis (DCA) to seamlessly and passively trace container components back to their original source, eliminating the need for tags, labels, and manual interventions.
WHY APIIRO
Enhance your application security with precise code-to-runtime mapping
Overcome the complexities of modern containerization and gain valuable insights by accurately linking runtime container images to their source code.
Comprehensive risk assessment
Identify and prioritize security issues by combining findings from both runtime and source code analysis. Ensure no vulnerabilities slip through the cracks.
Efficient remediation
Streamline the fix process by pinpointing exact locations in the source code repository where issues originate, even after complex transformations during the build process.
Enhanced ownership tracking
Easily trace container image ownership back to the responsible team by leveraging source control management (SCM) history, improving accountability and response times.
Deeper context for prioritization
Gain insights from runtime and source code analysis to better prioritize issues. For example, use code-level information about PII handling to prioritize runtime findings.
HOW IT WORKS
Leverage the power of Deep Code Analysis (DCA) for precise matching
Apiiro’s Code-to-Runtime Matching Technology uses advanced techniques to create accurate mappings between source code and container images, enhancing application security and development efficiency.
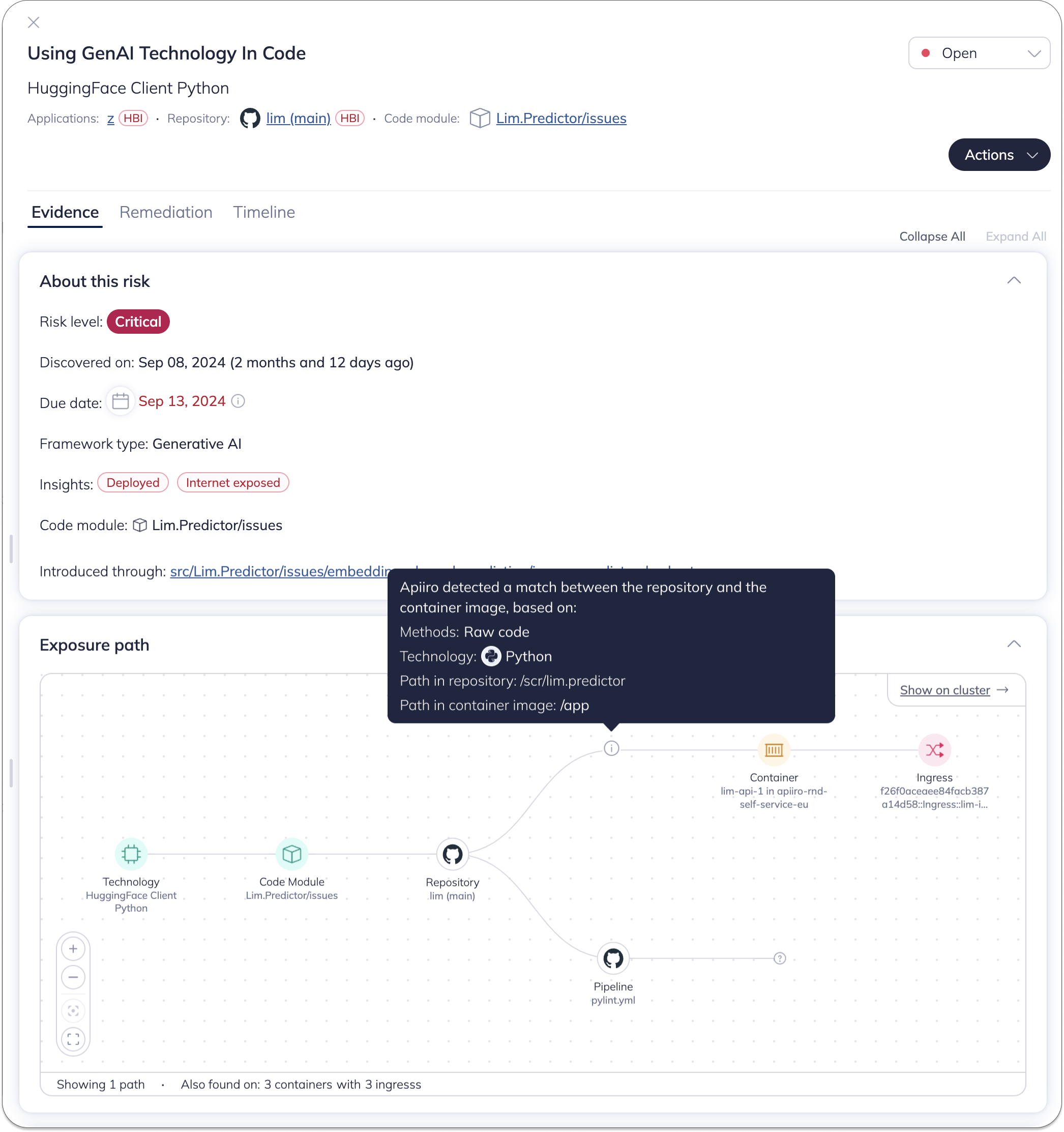
Applicative fingerprinting
Identify unique artifacts and metadata that can be reliably traced between source code and runtime container image. This approach provides extensive coverage while minimizing false positives.
Multi-layered analysis
Combine deep code structure insights with both strong and weak indicators to create highly accurate mappings. This comprehensive strategy mitigates risks associated with shallow or unreliable matches.


Language-specific techniques
Utilize tailored approaches for different programming languages. For example, in Java projects, extract metadata from pom.xml files and identify entry class names. For C# projects, focus on “hot spot” symbols likely to remain unique and untouched.
Agentless implementation
Perform all analysis using passive, read-only access, eliminating the need for intrusive agents or modifications to your existing infrastructure.

Monorepo support
Go beyond repository-level matching to pinpoint specific modules within large monorepos, addressing the challenges posed by complex project structures.
Continuous improvement
Leverage Apiiro’s expertise in DCA to continuously refine and enhance the matching process, ensuring accuracy even as containerization technologies evolve.


Revolutionizing Application Security: Apiiro Unveils Groundbreaking Code-to-Runtime Technology

Introducing Code-to-Runtime: Enriching AppSec with True End-to-End Visibility
Revolutionize your approach to application risk management and security
With Apiiro’s Code-to-Runtime Matching Technology, you can confidently trace container components back to their source, streamline your development process, and enhance your overall application security posture.

 Back
Back