Cookies Notice
This site uses cookies to deliver services and to analyze traffic.
📣 Introducing AI Threat Modeling: Preventing Risks Before Code Exists

 Back
Back

Unified risk and vulnerability management across application, infrastructure, and code quality scanners, with code-to-runtime actionable context
Automated security controls validation and assurance based on your organization’s SDLC policies, with actionable context from your CMDB
Risk Graph policy engine and developer’s guardrails at every phase: design, development (pull request), and delivery (build/deploy)
 Back
Back


On November 1st Dropbox informed the public about a breach the company suffered and discovered on October 14th. The incident involved targeting the company’s 130 private code repositories hosted on GitHub and included secrets such as credentials and API keys from those bespoke repositories. The breach also involved a leak of private information regarding Dropbox’s developers, customers, vendors and sales leads, as the company stated in the post linked above.
As this incident was investigated and tacked internally, we have limited information as to what has actually occurred. However, we can still learn from this particular story and recommend best practices to help prevent such incidents from happening at other organizations.
This is not the first time we see a very particular modus operandi such as this. The scheme consists of three steps:
In fact, this exact tactics was also employed in another recent attack on GitHub, just a month ago.
Here are the current (left) and previous (right) campaign emails side-by-side for comparison:
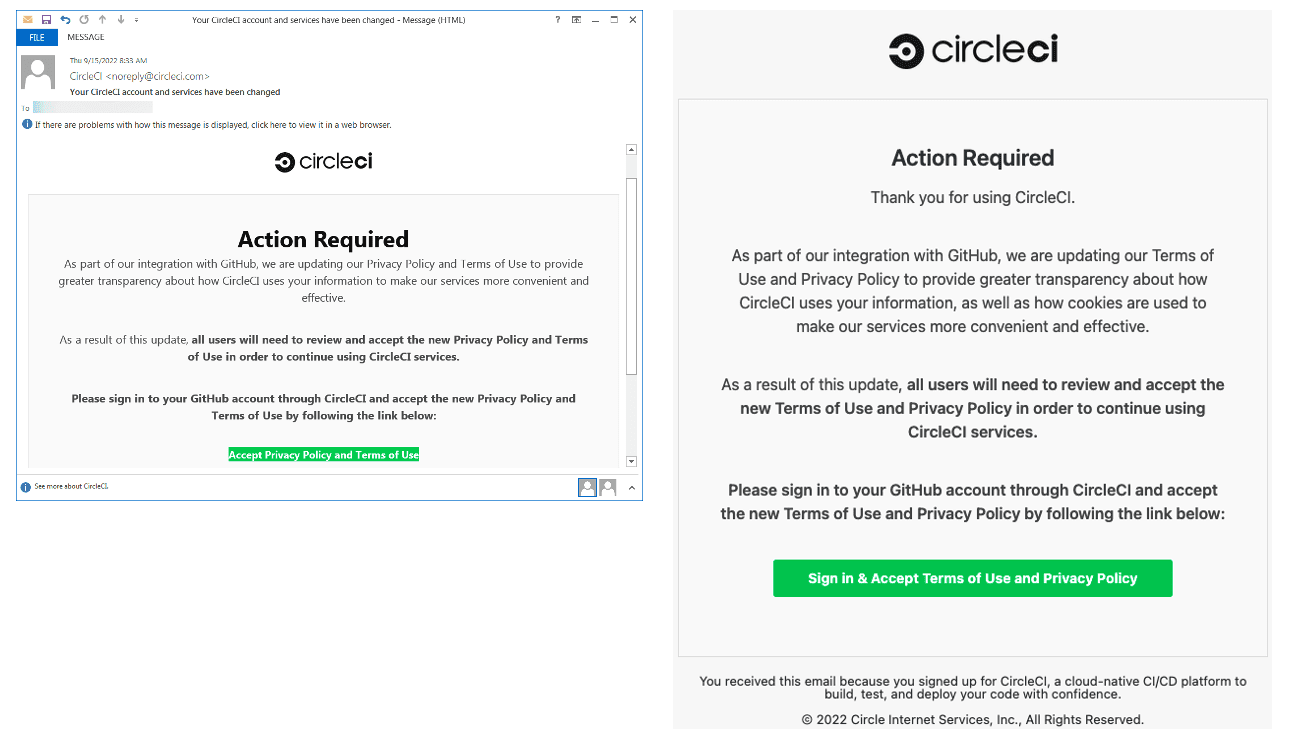
What’s also important to notice is that in order to hijack the account the fake phishing sites that the emails were leading to would request input of hardware-based one-time-password that the developer has and which, once acquired could have been used against the original site in order to successfully abuse it. This is an extra effort that was put into the scheme for it to succeed.
Back in June we published the report “Secrets Insights Across the Software Supply Chain”, in which we analyzed 25k+ of private repositories from various organizations and discovered that the likelihood of exposed secrets in private repositories is as high as eight times the number found in public repositories. Among other findings, we also discovered that the majority of secrets are found in formats typically used for configuration files, more than 40% of all the secrets are detected in YAML files, and more than 39% are in JSON files.
One important change mentioned by Dropbox is the use of a WebAuthn mechanism. This is because it includes a mechanism of origin-validation that is proved to be effective against phishing attempts.
Finally, one cannot neglect security awareness training and a practice of employing better phishing detection systems. This is not something to overlook, especially that the operational cost of conducting it is sometimes very low.
—
Keep in mind that when it comes to supply chain security and secrets in code, Apiiro can help! Apiiro provides real-time, continuous and contextual detection of secrets, with automated workflows so you can manage your code and your risk as new secrets are introduced. Our platform uses the latest algorithms for entropy detection of crypto keys and leverages our deep understanding of the code to evaluate the context of each secret we find in order to lower false positive rates and better prioritize each issue by business impact.
This site uses cookies to deliver services and to analyze traffic.
