TELECOM
Secure Software, Resilient Networks
Comprehensive Risk Visibility and Compliance for the Software-Defined Telecom Industry
Apiiro brings the rigor of enterprise-grade security—honed in finance, SaaS, and other regulated sectors—to meet the evolving demands of telecom networks.
WHY APIIRO FOR TELECOMMUNICATIONS
Secure Software Design for a Connected Telecom Industry
As the telecommunications sector expands with advancements like 5G, IoT, and cloud services, the landscape of cyber threats becomes increasingly complex. Maintaining a proactive application security posture is essential to protect sensitive data and ensure uninterrupted service.
- Accelerate Deployment Without Compromising Security: Apiiro enables rapid development cycles while embedding security throughout the software lifecycle.
- Early Risk Detection: Identify and mitigate vulnerabilities in the design phase, preventing issues before they escalate.
- Secure Development and Delivery: Design, develop, and deliver secure telecom applications for subscriber management, network orchestration, and billing.
- Balance Innovation and Risk: Rapidly adopt technologies like 5G and edge computing while maintaining compliance with telecom regulations and protecting critical network infrastructure.

Monitor Hundreds of Pull Requests Every Week
Track changes across network APIs, OSS/BSS systems, and cloud-native apps for full-stack visibility and secure deployments.
Reduce MTTR From Days to Minutes
Mitigate risks before they disrupt network availability, degrade service quality, or impact subscribers with real-time visibility and prioritization.
Manage Application Risk from One Place
Get near-instant visibility across your entire application portfolio and focus on the risk-affected areas that matter most.
“We’re finally fixing more vulnerabilities than we’re detecting—a huge milestone for us.”
We can see vulnerabilities in a single timeline—from code to runtime—without spending extra time mapping or tagging everything. It’s really helpful for both developers and our team to focus on prioritizing the most critical risks. ”


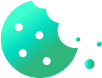
Improve Risk Visibility and Response
Using our patented deep code analysis (DCA), Apiiro creates a continuous application inventory–called the eXtended software bill of materials (XBOM)–that provides a clear view of vulnerabilities across telecom service APIs, subscriber databases, and core network applications.
This visibility helps prioritize and mitigate the highest risks to telecom infrastructure and customer data, ensuring compliance throughout the development lifecycle.
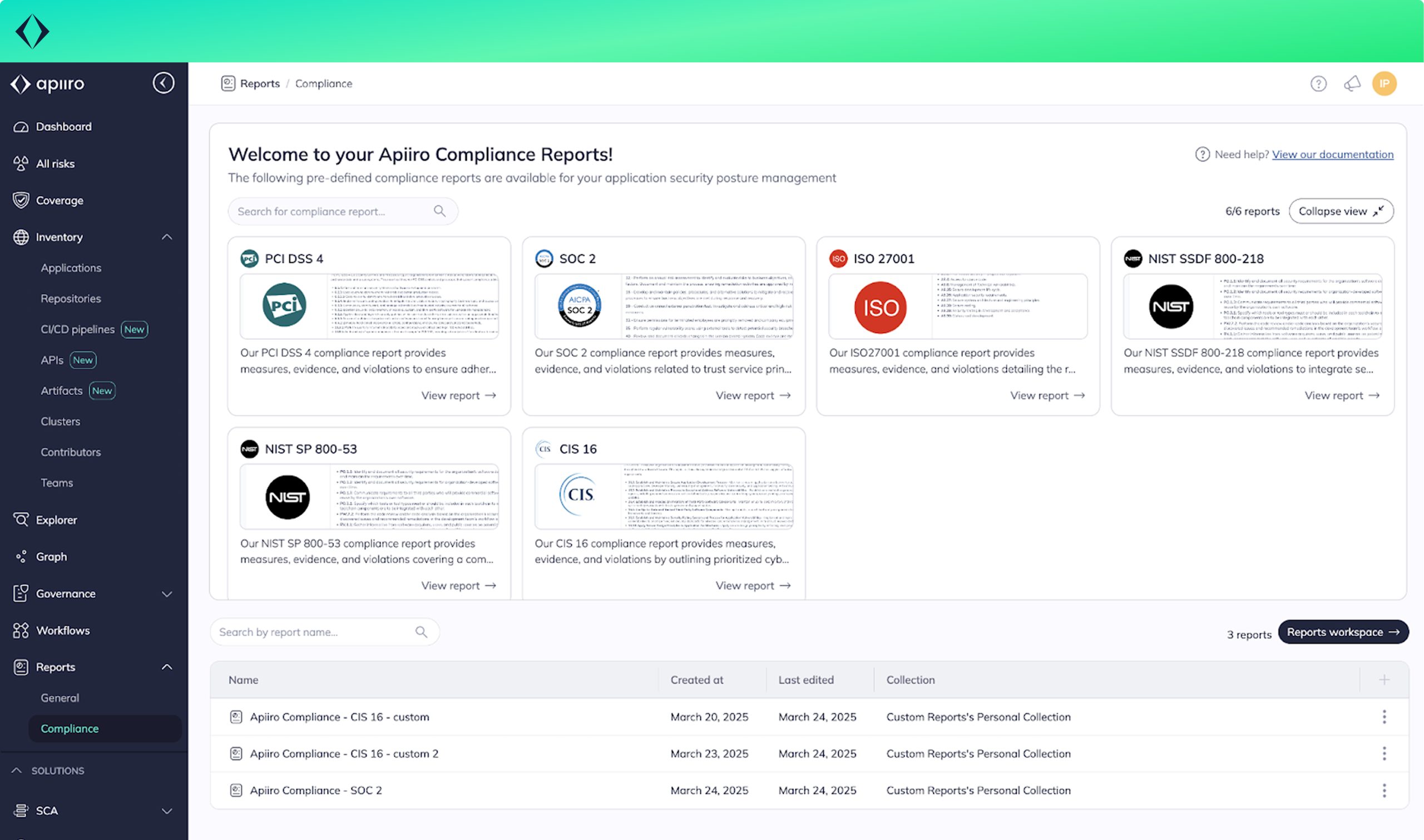
Automate Compliance for Telecom Regulations
Apiiro helps telecommunications providers comply with industry regulations such as FCC, GDPR, and NIST by automating material change detection and triggering relevant security actions.
This ensures critical network infrastructure and customer data remain protected while simplifying audit preparation with clear evidence of risk management.

Clarify Security Roles and Responsibilities
Clarify Security Roles and Responsibilities
Managing security roles across distributed telecom networks, numerous code repositories, and critical integrations like subscriber data platforms and network APIs can be a challenge.
Apiiro helps by mapping risks to specific teams, using features like OrgTeams to ensure clear ownership and accountability–without disrupting service innovation of deployment.
CUSTOMER STORY
Navan Automates Risk Assessments and Reduces Security Bottlenecks
- Achieved near-instant visibility into components, risks, and material changes across repositories and applications.
- Automated risk assessments and prioritization, replacing manual security reviews and alert triage across hundreds of weekly pull requests.
- Shifted application security earlier in the development lifecycle with actionable, risk-based developer guardrails.
“Apiiro recognizes and classifies risks in a way I have not seen any other company do.”

Keep your network open for business–closed to threats
Discover how Apiiro secures telecom applications from development to deployment.

 Back
Back